Overview
Electric vehicle (EV) chargers and software management systems communicate via the Open Charge Point Protocol (OCPP). It is governed by the Open Charge Alliance (OCA) which formally certifies products for compliance.
The security part of OCPP defines an end-to-end security design architecture, with implementation guidelines for both Charge Point and Central Management System. It was first introduced in 2018 and now is in its third revision.
System architecture
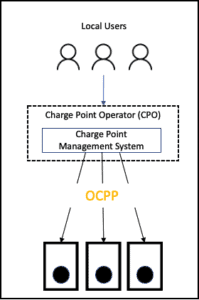
OCPP defines the communications path between a supported charger and a Charging Station Management System (CSMS). In many cases, the CSMS is a cloud-based platform. The charger and the CSMS communicate with Web Sockets (WS), a bi-directional HTTP-like protocol. When that channel is encrypted, the protocol is called Secure Web Socket (WSS), similar to HTTPS.
The OCPP security framework aims to define the security of this communications channel while using industry-standard best practices.
Security concepts
Like most communication network security frameworks, the OCPP security framework deals with the three most common security issues:
- Secrecy of communications – A well-defined system encrypts the communications between the entities so that unauthorized third parties cannot eavesdrop on the communications.
- Authentication of the server – the charger should easily verify it communicates with the right server. Failing to do that may result in a communication hijack to a rogue server.
- Authentication of the client – The server should be able to authenticate the charger to prevent attackers from creating fake chargers that impersonate real chargers and pollute the server database.
OCPP Security Profiles
The OCPP security architecture defines three levels of security profiles:
| Profile | Channel encryption | Server Auth | Charger Auth |
| Security Profile 1 | – | – | Password |
| Security Profile 2 | TLS 1.2 or higher | Server Certificate | Password |
| Security Profile 3 | TLS 1.2 or higher | Server Certificate | Client Side Certificate |
Security Profile 2 or Security Profile 3, or both must be implemented to receive OCPP Security implementation.
How OCPP security prevents common attack scenarios
Correct implementation of the OCPP Security profiles can protect against some of the more common attack scenarios as shown in the table below:
| Attack Name | Attack Details | Impact | Protection |
| Server hijack | A malicious server hijacks traffic from the charger.
This can be easily done by manipulating DNS entries in one of the DNS servers used by the charger. |
|
Security Profile 2 or Security Profile 3 eliminate this attack due to server auth. |
| Communications eavesdropping | Rogue player (e.g. router, proxy, etc.) records or manipulates unencrypted traffic between the charger and the server. |
|
Security Profile 2 or Security Profile 3 eliminate this attack due to channel encryption. |
| Charger impersonation | A fake charger simulator impersonates actual chargers and spams the server with fake data. The server can not distinguish between real and fake messages. |
|
Security Profile 1 or
Security Profile 2 or Security Profile 3 eliminate this attack due to client auth. |
Practical considerations
To receive OCPP Security implementation, Security Profile 2, Security Profile 3, or both must be implemented. In reality, most certified chargers elect to support Security Profile 2 since it is much easier to implement on embedded systems.
Security Profile 2 uses a shared key (password). The server and the charger must share this password before communication starts. It is recommended to use the following flow upon the initial connection of the charger to the server:
- The manufacturer of the Charge Point initializes it with a well-known default password. This can be a fixed password for all Charge Points or unique for a specific batch/customer. However, this default password must be known to the Charging Station Management Systems (CSMS).
- When the Charge Point connects to the CSMS for the first time, it uses the default password. It should then immediately update that password with a unique one.
- The CSMS randomly generates a unique password. It then securely saves this password in its database for that specific charger.
- A unique password is sent to the charger over the secure channel (wss).
- The charger will use this unique password for all follow-up communications, and the server will expect and verify it.
The procedure for updating the password in item 4 above is well-defined in the OCPP security documentation and is part of the security certification.
Summary
OCPP Security implementation is critical for the security and stability of any charger network. Operators should verify that the chargers and management systems they choose implement these important security measures.
The simplest way to verify compliance is via the OCPP Security certification badge. This badge is provided only to the best products that pass the rigorous certification process and is considered the gold standard of security in the EV charging space.



